 |
| Google introduces secure remote access service without VPN |
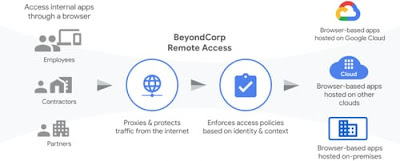
Due to the increasing number of employees working at home during holidays related to the development of Corona virus, Google introduced a new security service (BeyondCorp Remote Access) that allows the use of virtual private networks (VPN). Without remote access to internal systems. The company discovered how this energy can be absorbed for remote operation.
With cloud-based service (BeyondCorp remote access), employees can safely access corporate internal web applications from any device or site. That is why this new service was developed, secure and fast access to browser-based applications.
The service relies on a system that Google developed for internal use a decade ago, and the company said in an article: "It uses a method that usually requires different authentication before it can be given access to external resources permissions."
When the service started, it was time to act remotely to put pressure on the security of institutions and companies that find it difficult to adapt to their networks. (BeyondCorp Remote Access) is a technical company (like Google) that develops its internal projects and turns them into public resources (such as (Kubernetes)) or (Vitess).
Google has said that VPNs are a challenge today, and users who are not used to using VPNs as companies try to launch a large number of VPNs in a short period of time will find it difficult to use them.
The blogger said: "If the company wants to allow access to partners or contractors, it may be difficult to create a security group with restricted access rules, and when the number of connections suddenly increases, the VPN architecture may not be able to handle excessive stress."
BeyondCorp remote access service is designed for such situations. Since 2011 Google has been simplifying access to its network. This creates the service, which limits the number of users for each internal application. Specific access strategies become easy.
The service avoids the need for a VPN by designing a database for each device authorized to communicate, security certificates and personnel resources installed on the device, and information about user names and user names. Membership in database integration groups.
Employees can access the network remotely using the login system that authenticates itself via an internal database. This simplifies the process and eliminates the need to install or configure separate programs.